Continuous Authorization. Not audit panic.
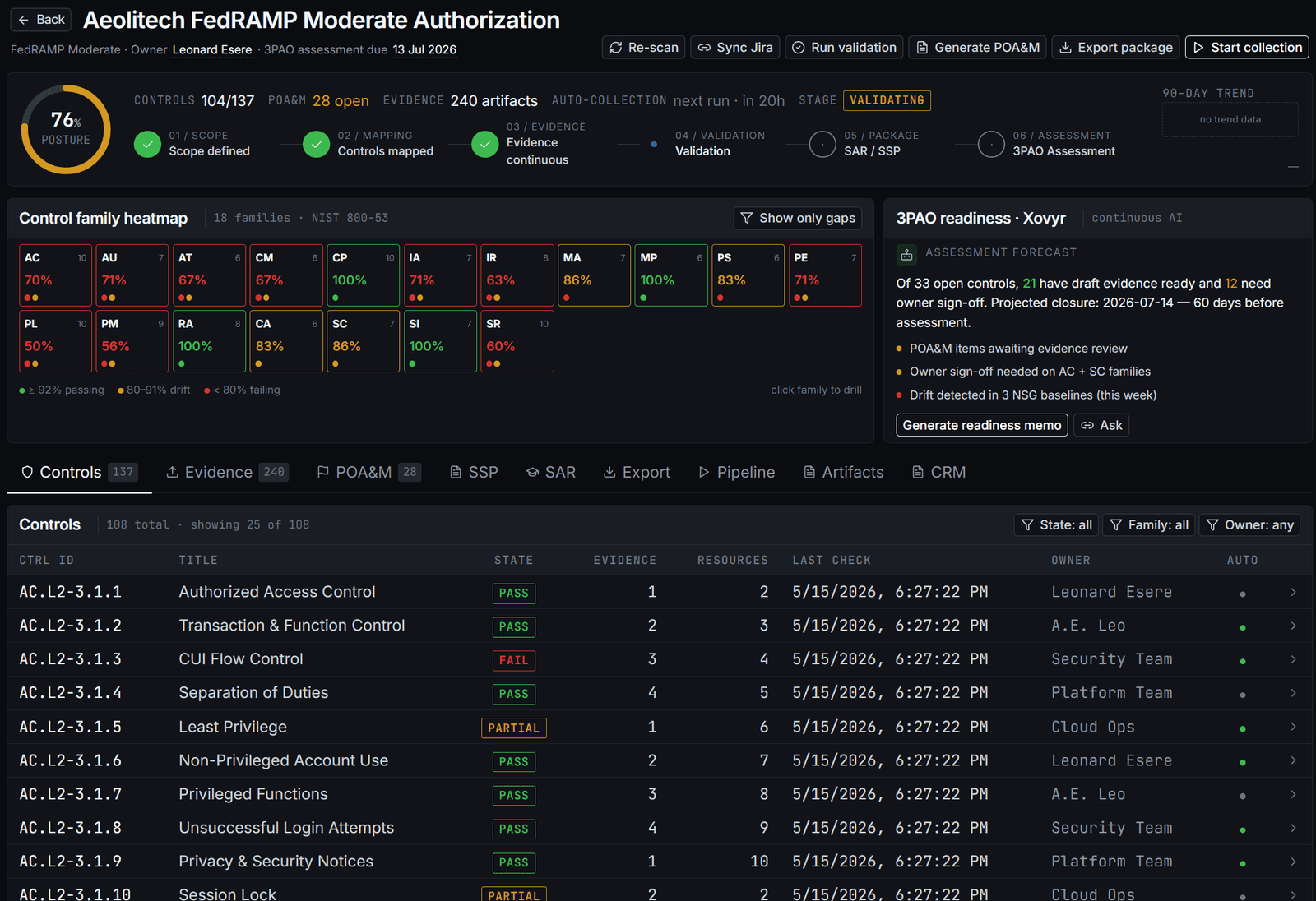
ATO has been a calendar event for two decades — a snapshot every three years and a 90-day scramble before each one. Continuous Authorization (cATO) is the conceptual shift the DoD CIO and FedRAMP PMO are pushing toward. PolicyCortex is built for it: evidence accrues, the package is always current, OSCAL is the substrate.
Three things change. The audit experience changes with them.
- 01FROM
Point-in-time assessment, 3yr re-cert.
TOContinuous posture, always assessment-ready.
Traditional ATO is a snapshot taken every 3 years and a 90-day scramble before each one. cATO maintains posture between assessments — the package is always current, not generated. Re-cert becomes a signature, not a project.
- 02FROM
Evidence collected by hand for the audit window.
TOEvidence emits as a byproduct of remediation.
Every closed finding ships a content-hashed evidence record. The SSP narrative for each control is the ordered concatenation of those records. Authoring stops. Accruing starts.
- 03FROM
SSP authored in Word. POA&M tracked in Excel.
TOOSCAL 1.1.2 native. Assessor ingests directly.
Word/Excel artifacts are downstream renderings. The substrate is OSCAL — Open Security Controls Assessment Language — the format DoD CIO + FedRAMP PMO + NIST OSCAL Project are converging on. Assessors with OSCAL tooling consume directly.
What an OSCAL record actually contains.
A control implementation in the OSCAL model is more than "PASS" or "FAIL." It carries the responsible team, the evidence link, the rollback ID, the hash, the implementation status, and cross-references to other framework citations.
The assessor doesn't open a Word doc. They ingest the JSON. Every claim is independently verifiable from the linked evidence.
{
"control-implementation": {
"uuid": "ci-AC-3-7-storage",
"control": "AC-3(7)",
"by-component": [
{
"component-uuid": "comp-storage-cui-prod-east",
"description": "Public access disabled · enforced via Azure Policy",
"implementation-status": "implemented",
"responsible-roles": ["platform-team"],
"links": [
{ "href": "evidence://ev-7c4a90", "rel": "evidence" },
{ "href": "rollback://rb-9f3a", "rel": "reversal" }
],
"props": [
{ "name": "last-validated", "value": "2026-05-15T14:22:11Z" },
{ "name": "hash", "value": "sha256:4b3a…ce19" },
{ "name": "framework-also", "value": "CMMC L2 AC.L2-3.1.2 · ISO A.5.15" }
]
}
]
}
}You inherit ~50% of controls from your CSP's P-ATO. Find out which.
A NIST 800-53 Moderate baseline has 89 controls. About half are fully inherited from the CSP's existing P-ATO. About a quarter are shared responsibility. The rest are yours. Knowing which is which collapses scope — and stops you from spending assessment time re-litigating controls the CSP already owns.
| PROVIDER | FULLY INHERITED | SHARED | YOU OWN | BASIS |
|---|---|---|---|---|
| Azure GovCloud | 47 | 23 | 19 | Microsoft FedRAMP P-ATO |
| AWS GovCloud | 51 | 19 | 18 | AWS FedRAMP H-ATO |
| GCP Assured WL | 44 | 27 | 17 | Google Assured Workloads |
● BASELINE NIST 800-53 R5 MODERATE · 89 SUB-CONTROLS PER ROW
What is cATO and why does it matter?
Continuous Authorization (cATO) replaces point-in-time assessment with ongoing posture. The DoD CIO's 2022 cATO memo + FedRAMP's Continuous Monitoring strategy both push this direction. The win: you're always assessment-ready instead of scrambling 90 days before re-cert, and the AO has a real-time view of risk instead of a stale snapshot.
Why OSCAL native instead of Word/Excel?
OSCAL (Open Security Controls Assessment Language) is the format DoD CIO, FedRAMP PMO, and NIST OSCAL Project are converging on. Native OSCAL means an assessor with OSCAL-aware tooling consumes the package directly. Word and Excel are downstream renderings we generate from the OSCAL source — not the other way around.
How does evidence inheritance work?
Most NIST 800-53 controls (~47–51 of 89 baseline Moderate sub-controls) are fully inherited from the CSP's existing FedRAMP P-ATO. PolicyCortex shows exactly which ones inherit, which are shared responsibility, and which you must implement. That's where the actual work is — and you don't spend assessment time re-litigating the rest.
What counts as an audit-ready package?
SSP (NIST SP 800-18 r1), POA&M (eMASS-format CSV/XLSX), SAR (NIST 800-53A), OSCAL Authorization Package (JSON, 1.1.2), Continuous Monitoring record (JSONL, hash-chained, 7y retention), and an auditor-grade ZIP that bundles all of the above. All current, all signed, regenerable to any historical timestamp.
Connect a cloud. Walk away with the package.
30 days, $15K flat. Boundary mapped, evidence pipeline running, OSCAL bundle in your hand by day 30.
