Fix it. Don't just flag it.
CSPMs find risk and hand it to a human. PolicyCortex closes the loop. Every action ships a matched captureState / restoreState pair — the runtime refuses to execute any remediation whose rollback path is undefined.
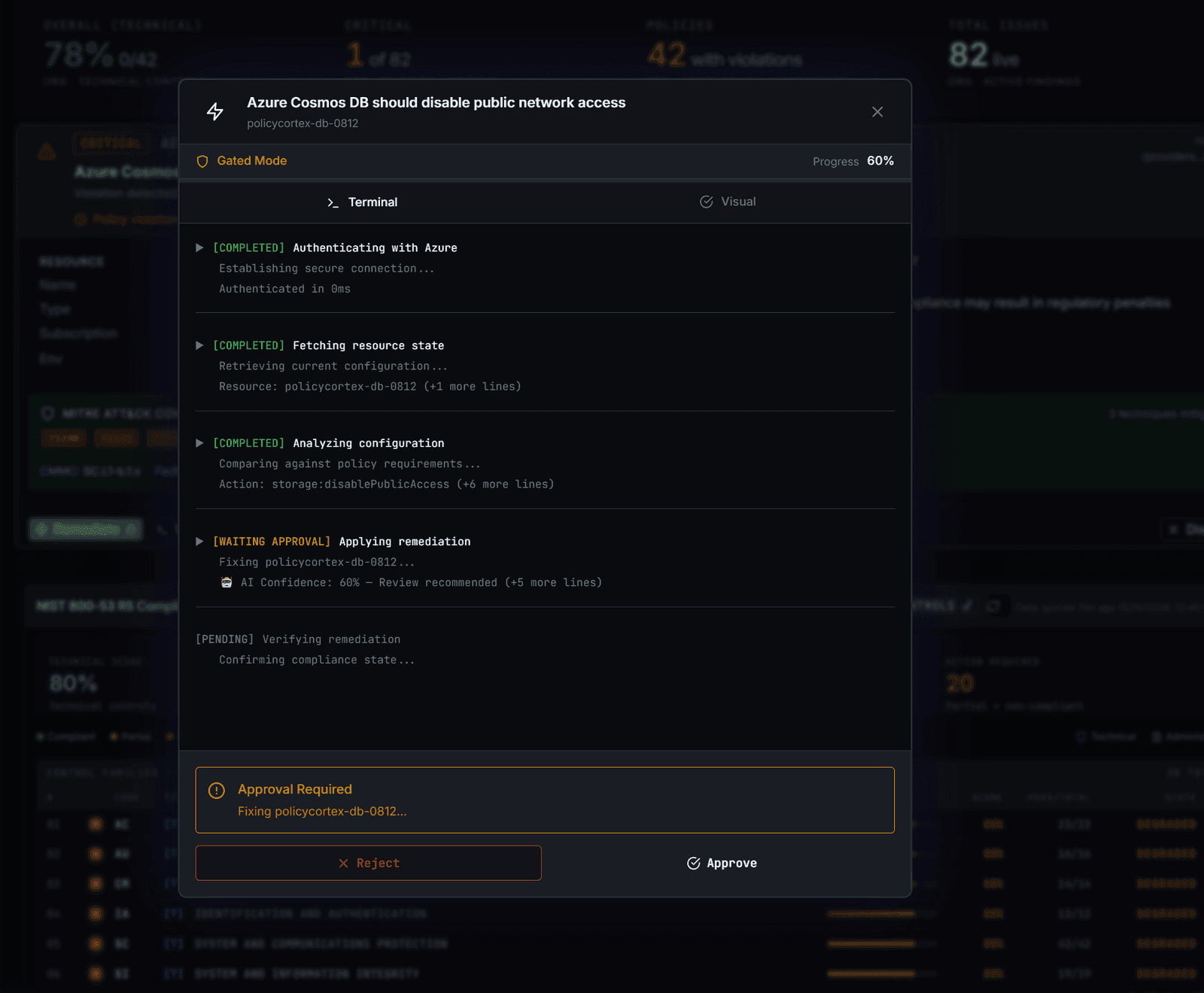
Three modes. Graduate when ready.
Engine drafts a remediation. Logs the plan + estimated blast radius. Does not execute. You read the trail.
- GATE
- 0 actions executed
- WHEN
- Days 1–7 · trust calibration
Engine drafts + executes only after explicit approval. Approval can be per-action, per-class, or per-control.
- GATE
- Approve / reject per action
- WHEN
- Default mode · most ops time
Engine executes without approval inside scoped policies. Rollback contract verified every time. Audit trail preserved.
- GATE
- Policy gates · 3/3 required
- WHEN
- Confidence ≥ 94% · high-volume drift
Six layers between drift and rollback ID.
- 00DETECT
Drift surfaces from continuous monitoring. Severity scored, control mapped.
- 01PRE-CHECK
Pre-flight: blast radius bounded, resource state pinned, policy ack verified.
- 02AI DECISION
Xovyr proposes captureState / restoreState pair. Confidence published.
- 03EXECUTE
Action lands. Cloud API ack captured. State delta hashed.
- 04VERIFY
Post-state validated against intent. Mismatch → automatic rollback.
- 05ROLLBACK ID
Every successful action ships a rollback ID. Reversible by single API call.
Every action has an inverse. Or it doesn't run.
interface RemediationHandler<R> {
captureState(target: R): Promise<State>
apply(target: R, intent: Intent): Promise<Delta>
restoreState(target: R, state: State): Promise<void>
verify(target: R, expected: Intent): Promise<Boolean>
}
// runtime guarantee
// captureState ∘ restoreState ≡ identity
// restoreState refuses if State.hash mismatchWhat is the Safety Sandwich?
Pre-execution validation (blast radius, resource state, policy compliance) and post-execution verification (state delta hashes match intent), wrapped around every remediation. If anything fails, automatic rollback engages. Patent-pending.
Can I require human approval before every remediation?
Yes — GATED is the default trust mode. Approval can be per-action, per-control class, per-resource type, or per-environment. Most teams stay in GATED indefinitely for high-impact control families and move to AUTONOMOUS only for narrow, well-tested classes.
What happens if a remediation fails?
Every remediation action ships a rollback ID. If post-state validation fails, rollback engages automatically. You can also trigger rollback manually at any time via API or the Command Center.
Does PolicyCortex modify production resources?
Only with explicit permission. You control which resource classes can be touched autonomously vs which require approval. Production is never touched without your configured approval workflow.
See the substrate. In your own cloud.
30 days, $15K flat. Connect a cloud, run in SHADOW mode for the first week, graduate to GATED — keep what works.
